HTTP Tunneling
Firewall-safe, seamless serial connections across the internet
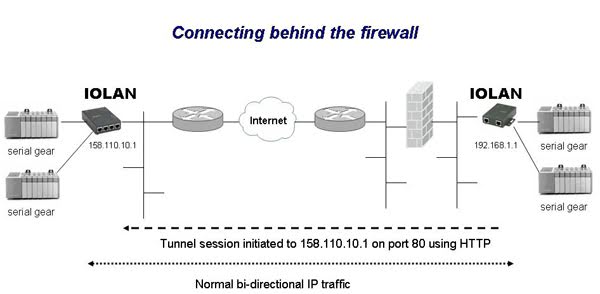
Connecting to remote serial communication based devices whether it is the serial console port on a piece of equipment or an industrial PLC is a simple matter when using a closed, dedicated network. By using a serial to ethernet device server such as a Perle IOLAN, serial data to and from the port are packetized onto ethernet packets and transported to a remote IP application or a peer IOLAN where it is converted back to serial for connection to the remote serial device peer. The IP address of all the elements involved are known and the client server relationship is clear.
When attempting to do this across the internet however, it is not as simple. In corporate environments, connections to the internet are safeguarded by firewalls, routers and proxy servers. The individual device IP addresses appear as a dynamic translated network address ( NAT ) to entities on the internet and are not directly addressable.
Firewalls are also very particular on the type of IP sessions that are allowed to and from the internet. Hypertext Transfer Protocol ( HTTP ) the standard used by Internet browsers operating under TCP port 80, is firewall-safe and is universally allowed to pass through. Other protocols such as SSH ( port 22 ) or Telnet ( port 23 ) are normally blocked. To allow these, the firewall configuration must be changed which compromises the existing corporate security policy.
By encorporating HTTP Tunneling technology, Perle IOLAN’s are the first and only serial device servers to securely connect and transport serial data for transport between remote serial peers over the internet without the need to change firewall settings.
This is how it works. A remote HTTP Tunneling IOLAN client behind a firewall establishes an HTTP session with an IOLAN server counterpart on the internet located in an enterprise DMZ ( De-Militarized Zone ) or Service Provider location. By utilizing standard HTTP GET and SET commands, these peers now have the ability to exchange packets. Serial data from an attached device can now be converted by the IOLAN and sent across the internet to its HTTP tunnel peer.
The IOLAN peer will then exchange the packet back to serial. The result is a firewall-safe, seamless serial connection through the internet.
HTTP Tunneling Feature Set
- Tunnel serial data over the internet with firewall-friendly HTTP Tunneling
- Send raw or encrypted data over HTTP port 80
- Send encrypted data over HTTPS port 443
- TCP and UDP sessions supported
- Can be used with HTTP proxies
- Run multiple simultaneous HTTP tunnels
- Operate both HTTP Tunneling clients and Server on the same IOLAN
- Transport data for IP-based devices across HTTP Tunnels
- Define which serial and IP-based equipment can connect across the tunnel
- The following IOLAN services can be used:
- Console Management ( Reverse Tel and Reverse SSH )
- TCP Sockets
- UDP Sockets
- Terminal Server ( Telnet, SSH, Rlogin )
- Trueport COM/port tty redirector traffic ( TCP )
- Printer traffic
- Serial tunneling ( serial port to serial port )
- Virtual modem
- Modbus Gateway ( TCP )
IOLAN HTTP Tunnel Relay
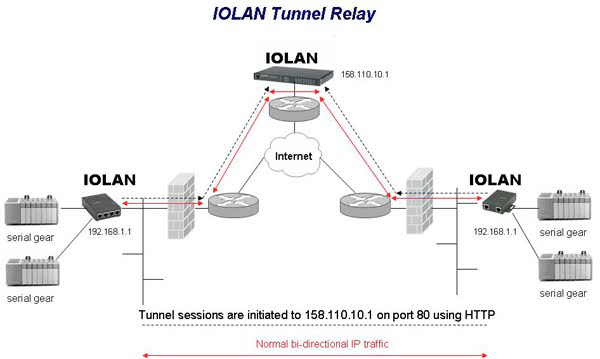
There may some applications where all of the end point devices are behind firewalls. Since firewalls will block any inbound connection from the internet, a tunnel relay component is required. An IOLAN located on an enterprise DMZ or Service Provider network and directly addressable on the internet is configured as an HTTP tunnel relay device. This IOLAN will then accept and associate the remote tunnel connections from the various end points and seamlessly pass IP traffic between them. Again, changes to the firewall are not necessary.
Besides a simple connection between serial ports across the internet, let us examine two other common scenarios.
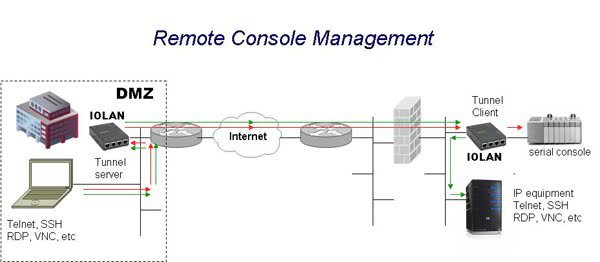
Console Management
IT administrators wishing to install terminal console servers at multiple remote branch locations to connect to equipment serial console ports can do so by using either the corporate network or the internet. Remote locations equiped with networks connected to the internet are normally protected by firewalls. This type of access using traditional console servers is not possible without “poking a hole” in the firewall to allow Telnet or SSH ( port 23 and 22 respectively ) inbound session requests from the internet. Doing this comprises the existing security policy and leaves the network susceptible to attack. Also the target console servers will likely have a dynamic NAT IP address making it difficult to address by a user on the internet.
Beyond traditional console servers, the more advanced Perle IOLAN has an HTTP Tunneling capability which enables direct Telnet or SSH connections to the IOLAN console server even when it is behind a firewall.
The remote IOLAN upon power up establishes an HTTP tunnel over port 80 to an internet addressable IOLAN at the head office location. The remote firewall allows this connection as the IOLAN operates within bounds of the established security policy by using firewall-friendly HTTP or HTTPS connections.
Administrators at the central site can now access the serial console ports at the remote branches by simply establishing a Telnet session to the local IOLAN in the DMZ. The remote IOLAN also provides a gateway connection to other IP-based devices where other adminstrative tools such as Telnet, SSH, RDP and VNC can be used.
If administrators are also connecting from behind a firewall, a tunnel relay IOLAN must be installed on the internet or enterprise DMZ to connect and pass IP traffic between the administrator workstation and remote devices.
Connecting a Serial-based application to remote serial ports
Another common scenerio involves connecting remote serial-based devices across the internet with a valuable legacy software application located in a central location. The software application needs to remain in place using the internet as the network for transport. By utilizing Perle IOLANs and Trueport, Perle’s com port redirector, this can be done.
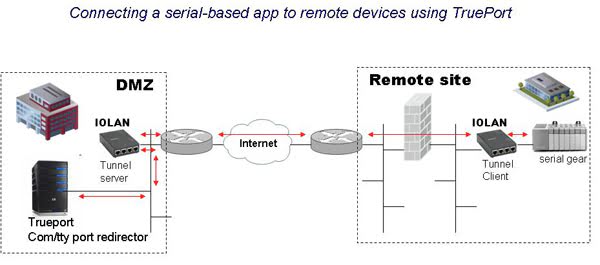
Connecting a TCP-based application to remote serial ports
In the similar way, an application on a central server that is TCP-based ( or UDP ) can also be used connect to remote serial devices across the internet. The central TCP application would simply send and receive packets using the local IOLAN gateway for tunneling to remote serial gear attached to an IOLAN peer.