
Defend against cybersecurity threats with these three tips
By Max BurkhalterJanuary 22, 2021
Do you have employees who now work remotely? Most hacks are due to a weakness at lower employee levels, which can be sealed with internal education and careful attention to who is accessing the network, when and from where in the world. However, employee education is just the first step. You need to follow through with concrete actions to make your network safer. Here are three ways you can help defend against cybersecurity threats
Update software across the board
Keeping software updated automatically is easier when everyone is working in a centralized location. With a distributed workforce, IT responsibilities may need to expand to include follow-up for security and stability of employee devices in use outside of the office. Security updates that are constantly pushed off or rescheduled can cause vulnerabilities. Give workers more ownership of their responsibility when it comes to protecting employer data and networks by teaching employees how to properly back up their systems, apply updates regularly and restore their systems if there is a failure after an update and they need to roll back.
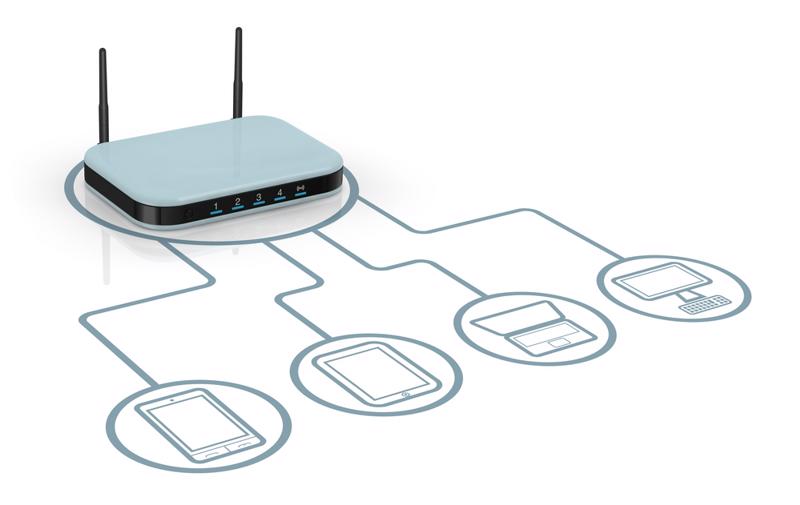
Keeping software continuously up-to-date is one of the most important things to do to stop hackers bent on accessing physical devices through an unprotected backdoor. Failure to apply a patch can leave your employee's computer vulnerable to attack. It's not just PCs that need updating. Mobile devices and applications need to be regularly updated, including operating systems. Routers in use should also be set to update automatically and to send an alert if an update fails. Secure routers are a must for remote workers who will be accessing company data.
Implement two-factor authentication
Adding an extra step or two to the login process can be a little tiresome, but it's the best way to stop common hacks based on password or usernames being compromised. By implementing two-factor authentication for logins to any company systems, employees will be required to enter a onetime code received through an alternate account or device or use a hardware token to finish logging in once their initial login credentials are submitted and approved.
This extra step could be receiving a code on their phone or via an email, and then entering that code on a secure screen. Many networks already have two-factor authentication as an option and it simply needs to be turned on. If not, your IT department can add two-factor authentication using an app to facilitate secure logins. Microsoft, Apple, and Google all have authenticators that can help secure your network from outside access by bad actors.
Track phishing scams
According to Microsoft, 91% of security breaches originate as email phishing attacks. Staying on top of company emails and monitoring the web for news of recent phishing attacks can help you prepare your entire organization from the C-suite to the data entry team about potential phishing scams and help them stay alert and on guard against emails that may not seem suspicious but are in reality an attempt at a breach. Remind staff that entering secure information in response to an email is almost always a no-go, and encourage them to check with IT or a superior if there is even the slightest bit of doubt.
Perle can help provide protection against on-site intrusions with industrial-grade networking and mainframe equipment that helps you circumvent bad actors. To learn more, read some of our customer success stories.



